IT Security
You will learn about firewall technologies, secure network architectures and forensic investigations, as well as how to analyse vulnerabilities in computer systems and identify malware. You will discover the creative methods used by hackers so that you can install effective protection mechanisms in the network, in server systems and mobile applications.
Software Security
You will learn about cutting-edge software architecture and design methods, allowing you to develop and implement secure software. You will delve into the topic of cryptography and implement software on various operating systems, both on the web and in the server, cloud and mobile domains. Artificial intelligence and machine learning are integral to analysing cyber-attacks and responding to unknown threats.
Security Management
In addition to special technical skills, you will also investigate standards in IT information security, risk management and methods of IT project and change management. You will also be introduced to the legal, social and ethical aspects of security management.
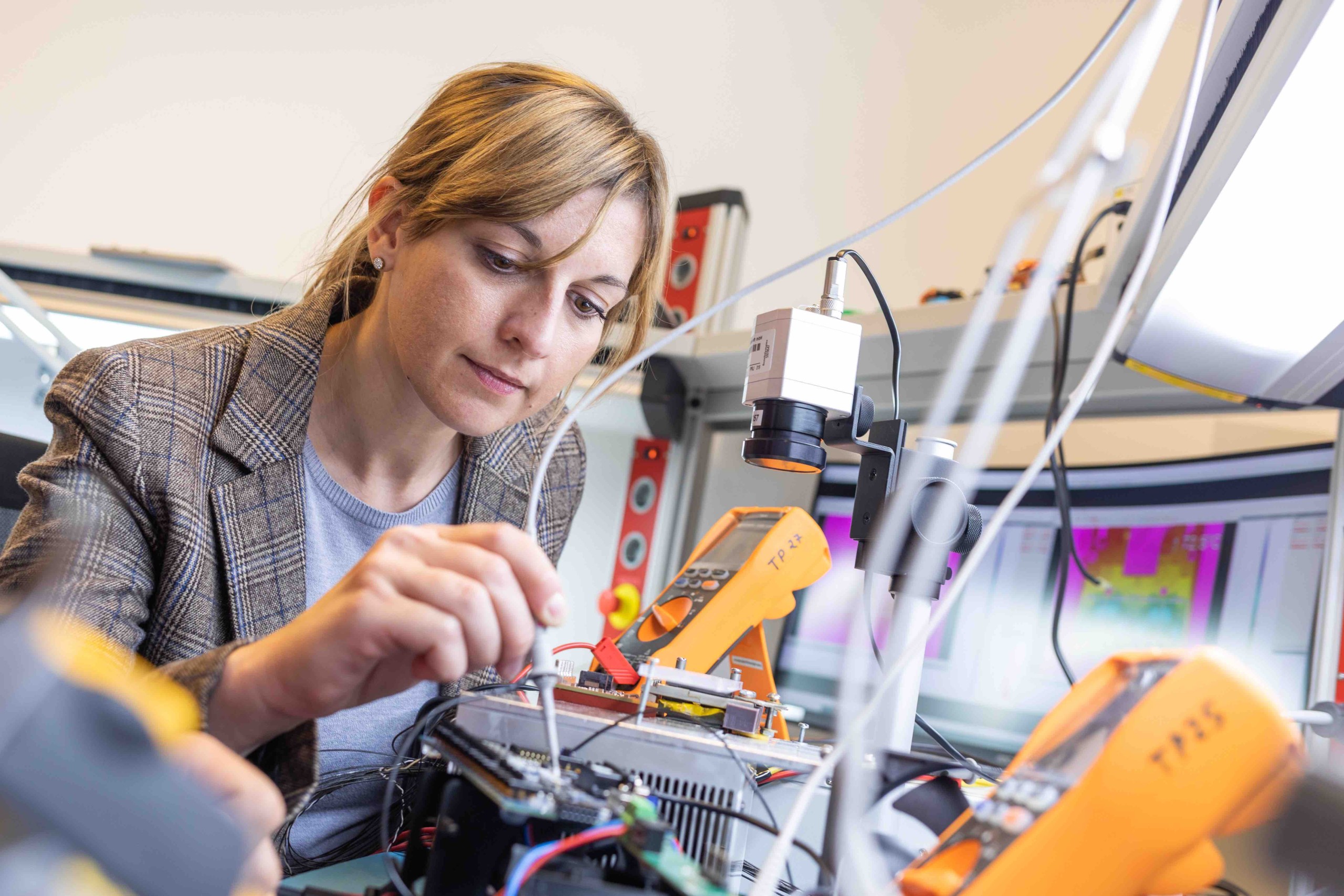
IT Security Practice
During the third semester you will undertake a project requiring you to apply your knowledge of IT and mobile security. As many of our students are already in employment, they can undertake projects related to their work.
You will further develop your knowledge of IT security during your Master’s thesis.